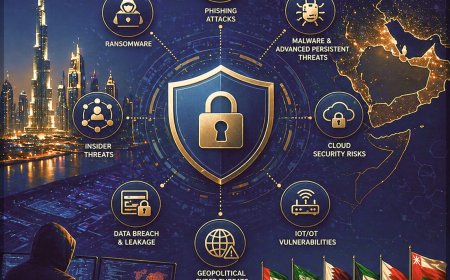
Top Cyber Threats Facing Middle East Enterprises & GCC Businesses
Explore top cyber threats in the Middle East and how CyberSec Consulting helps businesses prevent ransomware, APTs, phishing, and cloud security risks with advanced cybersecurity solutions.


Introduction
Cyber threats across the Middle East are accelerating at an unprecedented pace. Driven by rapid digital transformation, increased cloud adoption, and a complex geopolitical landscape, organizations across the GCC - including the UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain - are becoming prime targets for sophisticated cyberattacks.
According to IBM Security, the average cost of a data breach in the Middle East reached $7.46 million in 2023, significantly exceeding the global average of $4.45 million. This underscores the urgent need for enterprises to strengthen their cybersecurity posture, implement robust data protection strategies, and invest in advanced threat detection and response solutions.
Modern cybercriminals are no longer limited to data theft-they are launching ransomware attacks, disrupting critical business operations, and exploiting third-party and supply chain vulnerabilities to gain unauthorized access. For businesses across the Middle East and GCC region, the financial losses, regulatory penalties, and reputational damage from such cyber incidents can be severe.
This article explores the evolving cybersecurity threat landscape in the Middle East, highlighting key cyber risks affecting GCC enterprises, including ransomware, phishing, and supply chain attacks, along with actionable cybersecurity strategies to enhance resilience, ensure compliance, and protect critical digital assets.
Ransomware Attacks: A Rising Cybersecurity Threat in the Middle East

Ransomware remains one of the most critical cybersecurity threats impacting businesses worldwide. This type of malware attack encrypts an organization’s sensitive data, rendering systems inaccessible until a ransom is paid, often without any guarantee of full recovery. For enterprises, this creates a difficult choice between financial loss and operational disruption.
Why Middle East & GCC Businesses Are Prime Targets?
Ransomware attacks across the Middle East and GCC region, including the UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain, are increasing rapidly due to several high-risk factors:
- Heavy dependence on critical infrastructure sectors such as oil & gas, healthcare, and financial services makes them high-value targets for cybercriminals.
- Ongoing geopolitical tensions and cyber warfare activities are driving state-sponsored and organized cyberattacks.
- Accelerated digital transformation, cloud adoption, and remote work environments are significantly expanding the enterprise attack surface.
Financial & Operational Impact of Ransomware
According to Chainalysis, global ransomware payments surpassed $1 billion in 2024, with a notable share linked to attacks targeting Middle East organizations. However, the true cost of ransomware extends far beyond the ransom payment, including:
- Prolonged business downtime and operational disruption.
- Severe reputational damage and customer trust loss.
- Regulatory fines and compliance penalties.
- Long-term data recovery and incident response costs.
- Notable Ransomware Variants Targeting the Region.
Several advanced ransomware groups are actively targeting enterprises across the Middle East:
- LockBit - A leading Ransomware-as-a-Service (RaaS) platform known for fast, automated attacks.
- Conti - Focuses on large enterprises with highly coordinated cyber extortion campaigns.
- Clop - Specializes in data exfiltration and double extortion, threatening to leak sensitive data.
How to Prevent Ransomware Attacks: Best Practices?
To strengthen ransomware protection and enterprise cybersecurity resilience, organizations should implement:
- Endpoint Detection and Response (EDR) solutions for real-time threat monitoring and proactive attack prevention.
- Regular, secure offline backups to ensure fast recovery and business continuity.
- Employee cybersecurity awareness training, especially around phishing and social engineering attacks.
- Strong access controls, patch management, and zero-trust security frameworks.
Cloud Security Vulnerabilities: Rising Risks in Middle East Cloud Environments

The rapid adoption of cloud computing in the Middle East has transformed how businesses operate, delivering scalability, agility, and cost efficiency. However, this shift has also introduced significant cloud security vulnerabilities, exposing enterprises across the GCC (UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain) to data breaches, misconfigurations, and advanced cyber threats.
According to Gartner, 99% of cloud security failures by 2025 will be the customer’s responsibility, largely due to misconfigured cloud settings and weak identity access controls. This is particularly critical for organizations in the Middle East undergoing rapid digital transformation and cloud migration.
Common Cloud Security Risks Impacting GCC Enterprises
- Cloud Misconfigurations - One of the leading causes of cloud data breaches, including improperly configured storage buckets, databases, and access permissions. A study by Palo Alto Networks found that 65% of cloud breaches were linked to misconfigurations.
- Weak Identity & Access Management (IAM) - Poor access controls allow unauthorized users to access sensitive systems. The absence of Multi-Factor Authentication (MFA) significantly increases the risk of credential compromise.
- Data Encryption Gaps - Failure to implement end-to-end data encryption (both at rest and in transit) leaves critical business data vulnerable to interception and theft.
- Lack of Cloud Visibility & Monitoring - Without Cloud Security Posture Management (CSPM) and continuous monitoring, organizations struggle to detect anomalies, insider threats, and suspicious activities in real time.
Cloud Compliance & Regulatory Challenges in the Middle East
Governments across the region are enforcing strict cybersecurity compliance frameworks to ensure data protection and cloud security governance:
- Saudi Arabia National Cybersecurity Authority mandates robust cloud security controls and regulatory compliance standards
- UAE Cybersecurity Framework requires enterprises and cloud providers to implement advanced security measures and risk management practices
- Failure to comply with these regulations can result in financial penalties, legal consequences, and reputational damage for businesses operating in the GCC region.
Best Practices to Strengthen Cloud Security
To enhance cloud security posture and protect digital assets, organizations should adopt:
- Multi-Factor Authentication (MFA) to secure user access and prevent unauthorized logins
- Identity Governance and Administration (IGA) for robust access control and identity lifecycle management
- Cloud Security Posture Management (CSPM) tools to detect misconfigurations and ensure continuous compliance
- Zero Trust Security Framework to enforce strict verification across all users and devices
- Real-time threat monitoring and incident response solutions
Insider Threats: Hidden Cybersecurity Risks Within Middle East Organizations

Insider threats in cybersecurity are one of the most challenging risks for modern enterprises. These threats arise when employees, contractors, or third-party partners misuse their authorized access, either intentionally or accidentally - leading to data breaches, financial losses, and operational disruption. Unlike external cyberattacks, insider threats originate from within the organization, making them significantly harder to detect and prevent.
Why Insider Threats Are Increasing in the Middle East?
Cloud computing and digital transformation across the GCC region (UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain), organizations are facing a growing insider risk landscape. According to Ponemon Institute, insider threats have increased by 44% in the past two years, with an average cost of $15.38 million per incident, highlighting the urgent need for enterprise insider threat management.
Types of Insider Threats in Enterprise Security
- Malicious Insiders - Individuals who intentionally steal, leak, or sabotage sensitive data for financial gain or personal motives
- Negligent Insiders - Employees who unknowingly compromise security through weak passwords, phishing attacks, or poor cybersecurity practices
- Compromised Insiders - Legitimate user accounts that are hijacked by cybercriminals to gain unauthorized access to systems
Impact of Insider Threats on Middle East Businesses
- Data Breaches & Data Leakage - Exposure of sensitive information such as intellectual property, financial records, and customer data on the dark web
- Financial Loss & Compliance Penalties - Costs associated with regulatory fines, legal actions, and business disruption
- Reputational Damage - Loss of customer trust and brand credibility following insider-driven cyber incidents
Best Practices to Mitigate Insider Threat Risks
To strengthen insider threat detection and prevention strategies, organizations should implement:
- Data Loss Prevention (DLP) Solutions
Monitor and control data movement across networks and endpoints
Detect and prevent unauthorized data transfers and suspicious file-sharing activities - User Activity Monitoring & Behavior Analytics
Track employee actions to identify anomalies and suspicious behavior patterns
Leverage AI-driven security analytics for real-time insider threat detection - Strong Access Control & Identity Security
Enforce the principle of least privilege (PoLP) to limit unnecessary access
Implement Multi-Factor Authentication (MFA) for enhanced identity protection
Deploy Identity and Access Management (IAM) frameworks for centralized control - Supply Chain Attacks: Third-Party Cybersecurity Risks in the Middle East
Supply chain cyber attacks are rapidly emerging as one of the most dangerous enterprise cybersecurity threats. These attacks occur when cybercriminals exploit vulnerabilities in third-party vendors, software providers, IT service partners, or cloud platforms to infiltrate a target organization. Instead of attacking a well-protected enterprise directly, attackers compromise less-secure suppliers, using them as a gateway to access critical systems and sensitive data.
Why Supply Chain Attacks Are a Growing Threat in the Middle East?

Organizations across the GCC region, including the UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain. depend heavily on third-party ecosystems for cloud services, IT infrastructure, and digital transformation initiatives. This interconnected environment significantly increases cyber risk exposure:
- A study by Symantec found that 62% of global cyberattacks involved a third-party vendor.
- According to PwC, 56% of Middle East businesses experienced vendor-related cyber incidents.
- Critical sectors such as oil & gas, banking, and smart city infrastructure are prime targets for software supply chain attacks and third-party breaches.
Major Supply Chain Cyber Attacks Impacting the Region
- SolarWinds Breach - Attackers injected malicious code into trusted software updates, compromising thousands of organizations globally, including Middle East enterprises
- Kaseya Ransomware Attack Exploited IT management software to launch widespread ransomware attacks affecting multiple businesses.
- Nobelium & APT34 Campaigns - State-backed threat actors targeting financial services and energy sectors through compromised vendors and cloud providers
How Cybercriminals Exploit Supply Chains?
- Compromised Software Updates - Injecting malicious code into legitimate updates to gain system access
- Third-Party Credential Theft - Stealing vendor login credentials to infiltrate enterprise networks
- Weak Vendor Security Controls - Exploiting smaller suppliers with inadequate cybersecurity frameworks
Best Practices to Prevent Supply Chain Cyber Attacks
To strengthen third-party risk management and supply chain security, organizations should adopt a proactive cybersecurity approach:
- Vendor Risk Assessment & Compliance
- Conduct thorough third-party security assessments before onboarding vendors.
- Perform regular security audits and compliance checks
- Ensure adherence to regional frameworks, such as the Saudi Arabia National Cybersecurity Authority guidelines.
- Zero Trust Security Model
- Implement Zero Trust architecture - never trust, always verify.
- Enforce Multi-Factor Authentication (MFA) for all third-party access.
- Restrict vendor access in accordance with the least privilege principle.
- Continuous Monitoring & Threat Detection
- Use real-time threat intelligence and security monitoring.
- Deploy Endpoint Detection and Response (EDR) to identify suspicious activities.
- Enable automated patch management to prevent software supply chain vulnerabilities.
Phishing & Social Engineering Attacks: Leading Cybersecurity Threats in the Middle East

Phishing attacks and social engineering tactics continue to be among the most effective and widely used cyberattack methods targeting businesses globally. These attacks rely on deceptive emails, fake websites, and manipulated communications to trick employees into revealing sensitive information, login credentials, or financial data, leading to serious data breaches and account compromise.
Targeted Phishing Attacks on Middle East Executives
In the Middle East and GCC region - including the UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain-targeted phishing campaigns are on the rise. A particularly dangerous form, known as “whaling attacks” (executive phishing), specifically targets senior executives and decision-makers to exploit their high-level system access and authority for financial fraud, data theft, and business email compromise (BEC).
Why Phishing Attacks Are Increasing in the GCC Region?
- Rapid digital transformation and remote work adoption are expanding the attack surface
- Increased reliance on email communication and cloud-based collaboration tools
- Lack of cybersecurity awareness training among employees
- Growing use of AI-driven phishing attacks and advanced social engineering techniques
- Best Practices to Prevent Phishing & Social Engineering Attacks
- To strengthen enterprise email security and phishing protection, organizations should implement:
Security Awareness Training Programs
Educate employees on identifying phishing emails, malicious links, and social engineering tactics, and encourage prompt reporting.
- Advanced Email Security Solutions
Deploy AI-powered email filtering, anti-phishing tools, and threat detection systems to block malicious emails before they reach users. - Single Sign-On (SSO) with Strong Authentication
Simplify user access while maintaining security through SSO combined with Multi-Factor Authentication (MFA) - Continuous Monitoring & Threat Intelligence
Use real-time threat intelligence and security analytics to detect and respond to phishing campaigns.
Advanced Persistent Threats (APTs): Targeted Cyber Espionage Risks in the Middle East

Advanced Persistent Threats (APTs) represent some of the most sophisticated cybersecurity attacks facing modern enterprises. Unlike conventional cyberattacks focused on quick financial gain, APTs are long-term, targeted cyber espionage campaigns designed to infiltrate systems, maintain persistent access, and extract sensitive data over time. These attacks are often state-sponsored or executed by highly organized cyber threat groups, making them a major concern for enterprise cybersecurity in the Middle East.
Why Middle East & GCC Organizations Are High-Value Targets?
The Middle East cybersecurity threat landscape continues to evolve due to the region’s geopolitical significance and reliance on critical sectors. Organizations across the UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain face elevated risks due to:
- Government and public sector entities are being targeted for intelligence gathering and political surveillance.
- Financial institutions and banking systems are facing attacks aimed at stealing financial data and customer information.
- The energy and oil & gas industries are becoming prime targets due to their global economic importance.
- Rapid digital transformation, cloud adoption, and smart infrastructure initiatives are increasing the attack surface.
- Notable APT Groups Targeting the Middle East.
Several advanced threat actors are actively conducting cyber espionage and targeted attacks across the region:
- APT33 (Elfin Group) - Associated with attacks on aerospace, defense, and energy sectors.
- APT34 (OilRig) - Known for targeting government and financial organizations with espionage campaigns.
- MuddyWater - Specializes in long-term infiltration and data exfiltration using stealthy malware techniques.
Common APT Attack Techniques
These threat groups leverage advanced and evolving tactics, including:
- Spear Phishing Attacks - Highly targeted emails designed to steal credentials and gain initial access.
- Zero-Day Exploits - Exploiting unknown software vulnerabilities before patches are available.
- Custom Malware & Advanced Payloads - Tailored malicious code designed for persistence and stealth.
Defense Strategies Against APT Attacks
To strengthen enterprise cybersecurity and protect against APT threats, organizations should implement:
- Network Segmentation to limit lateral movement within IT environments.
- Threat Intelligence and Continuous Monitoring for real-time detection of advanced cyber threats.
- Zero Trust Security Architecture, ensuring strict identity verification for users and devices.
- Advanced Endpoint Protection and SIEM solutions for proactive threat detection and incident response.
How CyberSec Consulting Helps Prevent Cyber Attacks in the Middle East?

CyberSec Consulting delivers end-to-end cybersecurity services and managed security solutions designed to help enterprises across the Middle East and GCC region proactively defend against evolving cyber threats. With deep expertise in enterprise security, cloud security, and threat intelligence, CyberSec enables organizations to build a resilient and future-ready cybersecurity posture.
Comprehensive Cybersecurity Protection Approach
- Advanced Threat Detection & Response
Implementation of EDR, SIEM, and SOC services for real-time monitoring, threat hunting, and rapid incident response to stop ransomware, APTs, and advanced attacks. - Cloud Security & Compliance Solutions
Deployment of CSPM, IAM, and Zero Trust frameworks to secure cloud environments, prevent misconfigurations, and ensure compliance with regional regulations. - Identity & Access Management (IAM)
Strong identity governance, MFA, and least privilege access controls to prevent unauthorized access and insider threats. - Security Awareness & Phishing Simulation Training
Interactive LMS-based cybersecurity training programs with phishing simulations to reduce human risk and improve employee awareness. - Third-Party Risk & Supply Chain Security
Vendor risk assessments, continuous monitoring, and Zero Trust implementation to secure third-party ecosystems. - Cybersecurity Governance & Compliance
Alignment with regional frameworks such as NCA and UAE cybersecurity regulations, ensuring regulatory compliance and risk management.
Conclusion

As cyber threats continue to grow in scale and sophistication across the Middle East, businesses must adopt a proactive, layered cybersecurity strategy. From ransomware and APTs to cloud vulnerabilities and insider threats, the risk landscape demands continuous monitoring, advanced security controls, and employee awareness.
CyberSec Consulting empowers organizations with enterprise-grade cybersecurity solutions, managed services, and strategic consulting to mitigate risks, ensure compliance, and protect critical digital assets. By combining technology, expertise, and proactive defense strategies, CyberSec helps businesses stay ahead of cyber threats and build long-term cyber resilience.
Protect your organization from evolving cyber threats with CyberSec’s advanced cybersecurity services and solutions.
Connect with CyberSec Consulting today to strengthen your security posture, ensure compliance, and safeguard your business from cyber risks.
Get in touch now for a cybersecurity assessment and customized security strategy.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0