Modern Authentication Methods for Enterprises: Boost in 2026
Discover the best authentication methods for businesses in 2025. Learn how MFA, SSO, passwordless authentication, and IAM solutions improve cybersecurity, protect digital identities, and prevent data breaches.


Introduction
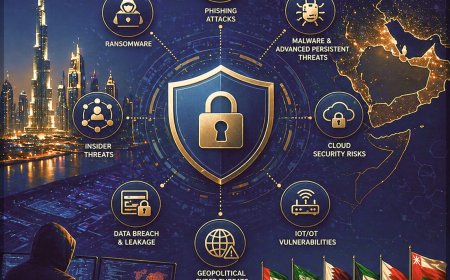
Cyber threats have become a constant challenge for modern businesses. Ransomware attacks, phishing campaigns, credential stuffing, and data breaches are impacting organizations of every size. Growing startups and global enterprises alike must prioritize cybersecurity to protect sensitive data, secure digital identities, and maintain business continuity. One of the most critical layers of defense in any cybersecurity strategy is implementing secure authentication for business.
Selecting the best authentication method is not just a technical choice - it is a strategic decision that influences user experience, regulatory compliance, identity security, and long-term scalability. A wide range of authentication methods for businesses, including multi-factor authentication (MFA), biometric authentication, and Identity and Access Management (IAM) solutions, can make the selection process complex without proper guidance.
This guide explores the most effective authentication methods, highlights their strengths and limitations, and provides a clear framework for choosing the right authentication solution for your organization. Businesses evaluating modern authentication strategies or upgrading existing systems can use this resource to strengthen access control, reduce cyber risk, and build a robust cybersecurity posture aligned with evolving digital threats.
Understanding Authentication: Importance of Secure Identity Verification in 2026

Authentication is the foundation of cybersecurity, ensuring that users are verified before accessing systems, applications, or sensitive data. Every login attempt must confirm identity accurately, as weak authentication mechanisms often become the biggest vulnerability in an organization’s security framework.
Growing reliance on digital platforms, hybrid work environments, and cloud-based infrastructure has made business authentication solutions more critical than ever. Rising cyber threats such as phishing, credential theft, and identity-based attacks demand stronger identity verification methods. Modern security frameworks like Zero Trust Security and Multi-Factor Authentication (MFA) are now essential components for protecting digital identities and meeting regulatory compliance requirements.
Effective authentication goes beyond compliance - it plays a key role in preventing data breaches, securing access control, and enhancing overall cybersecurity posture. Poor authentication practices can lead to unauthorized access, financial losses, and reputational damage. At the same time, overly complex login processes can disrupt user experience and reduce productivity.
Balancing security and usability is crucial. Strong authentication methods such as biometric authentication, adaptive authentication, and Identity and Access Management (IAM) solutions help organizations protect sensitive data while ensuring seamless and secure user access across systems.
Types of Authentication Methods

Authentication methods for businesses continue to evolve, offering a wide range of options based on security level, user experience, and implementation complexity. Modern organizations must evaluate different authentication solutions such as Multi-Factor Authentication (MFA), biometric authentication, passwordless authentication, and Identity and Access Management (IAM) systems to strengthen cybersecurity and protect digital identities.
Every business has unique security requirements, making it essential to choose authentication methods that align with risk management, compliance standards, and scalability needs. Factors such as ease of use, threat protection, and integration with existing IT infrastructure play a critical role in selecting the right authentication strategy.
Below is an overview of the most widely used and high-performing authentication methods in 2026 that help organizations enhance access control, prevent unauthorized access, and improve overall cybersecurity posture.
Password-Based Authentication
- Password-based authentication remains the most commonly used method in business environments, but also one of the most vulnerable. Weak passwords, credential reuse, and a lack of security controls expose systems to cyber threats such as brute-force attacks, phishing, and credential stuffing. This makes it a high-risk approach in modern cybersecurity frameworks.
- Implementation is simple and widely accepted by users, making it convenient for quick deployment across applications and systems. Familiarity and low cost make it a preferred choice for basic access control, especially in environments with minimal security requirements.
- Security limitations become significant without additional layers like Multi-Factor Authentication (MFA) or Identity and Access Management (IAM). Poor password hygiene can lead to unauthorized access, data breaches, and compromised digital identities, impacting overall network security.
- Best suited for low-risk systems where speed and ease of access are prioritized over strict security controls. Modern cybersecurity best practices strongly recommend combining password-based authentication with advanced authentication methods to ensure stronger identity protection and business security.
Multi-Factor Authentication (MFA)
- Multi-Factor Authentication (MFA) strengthens cybersecurity by requiring multiple verification factors, including passwords, security tokens, and biometric authentication. This layered approach enhances identity verification and significantly reduces the risk of unauthorized access across business applications and IT systems.
- Strong protection against cyber threats such as phishing attacks, credential theft, and account takeover makes MFA a critical component of modern authentication solutions. Combining multiple authentication factors improves access control and safeguards sensitive business data.
- Implementation can sometimes impact user experience if not designed properly, especially when additional steps slow down login processes. Seamless integration with adaptive authentication and single sign-on (SSO) solutions helps balance security and usability.
- Ideal for organizations handling sensitive data, financial transactions, or regulated information. MFA has become a baseline requirement in cybersecurity frameworks, playing a vital role in Zero Trust Security models and enterprise identity and access management (IAM) strategies.
Single Sign-On (SSO)
- Single Sign-On (SSO) enables users to authenticate once and securely access multiple applications and systems without repeated logins. This approach improves identity management, simplifies access control, and enhances user experience across enterprise IT environments.
- Streamlined authentication reduces password fatigue, minimizes login issues, and improves productivity for employees managing multiple platforms. Fewer passwords also lower the risk of weak credentials and improve overall cybersecurity hygiene.
- Centralized access can become a risk if credentials are compromised, potentially exposing multiple systems at once. Strong security controls such as Multi-Factor Authentication (MFA), adaptive authentication, and Zero Trust Security frameworks are essential to mitigate these risks.
- Ideal for medium to large enterprises seeking scalable authentication solutions and improved operational efficiency. Combining SSO with advanced identity and access management (IAM) and passwordless authentication strengthens security while maintaining seamless user access.
Passwordless Authentication
- Passwordless authentication is transforming modern cybersecurity by eliminating traditional passwords, which are often the weakest link in identity security. Advanced authentication methods such as biometric authentication, hardware security tokens, and secure magic links enhance user verification and reduce risks of credential theft.
- A seamless and frictionless login experience improves user productivity while minimizing attack surfaces associated with passwords. Reduced dependency on passwords helps prevent phishing attacks, brute-force attempts, and credential stuffing, strengthening overall access control and network security.
- Initial implementation may require investment in compatible infrastructure, authentication platforms, and integration with existing Identity and Access Management (IAM) systems. Proper deployment ensures scalability, improved user experience, and long-term cybersecurity resilience.
- Ideal for organizations focused on future-ready security, digital transformation, and Zero Trust Security frameworks. Passwordless authentication is rapidly becoming a leading trend in enterprise cybersecurity, offering secure, scalable, and user-friendly access management solutions.
Essential Factors for Choosing Secure Authentication Solutions in 2026

Selecting the best authentication method for your business requires a strategic approach aligned with cybersecurity goals, industry requirements, and risk management priorities. No single authentication solution fits every organization, as security needs vary across cloud-based startups, healthcare systems, financial institutions, and enterprises handling sensitive data. Different industries demand tailored authentication strategies based on compliance standards, data sensitivity, and operational complexity.
Authentication methods such as Multi-Factor Authentication (MFA), Single Sign-On (SSO), passwordless authentication, and Identity and Access Management (IAM) must be evaluated based on scalability, user experience, and threat protection capabilities. Choosing the right authentication solution in 2026 involves balancing strong access control with a seamless user experience while ensuring protection against cyber threats like phishing, credential theft, and unauthorized access. Key factors such as regulatory compliance, integration with existing IT infrastructure, and long-term cybersecurity strategy play a critical role in decision-making.
Below are the essential factors organizations should consider when selecting secure, scalable, and future-ready authentication methods for business security.
Business Size and Organizational Complexity
- Business size and operational structure directly influence the choice of authentication methods and cybersecurity solutions.
- Small teams may rely on basic authentication, while large enterprises require scalable identity and access management (IAM) systems.
- Organizations managing multiple departments, remote workforces, and third-party access need advanced authentication strategies to ensure secure access control and data protection.
- Enterprise environments benefit from combining Single Sign-On (SSO) with Multi-Factor Authentication (MFA) to balance seamless user experience with strong cybersecurity and threat prevention.
Type of Data and Sensitivity Level
- Data sensitivity plays a critical role in selecting secure authentication methods for business. Systems handling financial data, customer information, or intellectual property require advanced identity security and data protection measures.
- Industries such as healthcare, finance, and e-commerce must implement strong cybersecurity controls to prevent data breaches, unauthorized access, and compliance violations.
- Certificate-based authentication and advanced encryption methods provide secure communication, data integrity, and enhanced trust for high-value transactions and system interactions.
Compliance and Regulatory Requirements
- Regulatory compliance is a key driver for adopting secure authentication solutions in modern cybersecurity frameworks. Standards such as GDPR, HIPAA, and PCI-DSS require strong identity verification and access control mechanisms.
- Multi-Factor Authentication (MFA), Zero Trust Security, and robust IAM solutions are often mandatory to meet compliance and audit requirements.
- Aligning authentication strategies with regulatory standards helps organizations avoid penalties, strengthen data protection, and maintain business credibility.
User Experience and Authentication Efficiency
- User experience is a critical factor in authentication strategy, as complex login processes can reduce productivity and increase security risks through workarounds.
- Low-friction authentication methods such as passwordless authentication, biometric authentication, and adaptive authentication improve usability while maintaining strong security.
- Customer-facing platforms especially benefit from seamless authentication experiences that enhance engagement without compromising cybersecurity.
Cost, Scalability, and IT Infrastructure
- Budget constraints and existing IT infrastructure influence the selection of authentication solutions and cybersecurity investments.
- Cloud-based authentication platforms offer scalable, cost-effective solutions for businesses seeking advanced security without heavy infrastructure costs.
- Evaluation of implementation, maintenance, and integration costs ensures long-term sustainability and effective cybersecurity management.
Integration with Existing Systems and Technology Stack
- Seamless integration with existing IT systems, applications, and identity management platforms is essential for effective authentication deployment.
- Compatibility with enterprise ecosystems such as cloud platforms, CRMs, and internal tools ensures smooth operations and improved efficiency.
- Modern authentication solutions offering APIs, plug-ins, and flexible integration capabilities enable faster deployment, better user adoption, and improved return on investment (ROI).
Top Authentication Practices for Businesses in 2026

Strong authentication strategies require continuous improvement, monitoring, and adaptation to evolving cyber threats. Effective business authentication solutions must be proactively managed to ensure long-term cybersecurity, data protection, and compliance.
Implement Layered Authentication for Strong Security
- Layered authentication combining Multi-Factor Authentication (MFA), Single Sign-On (SSO), and passwordless authentication enhances identity security and reduces single points of failure.
- Adaptive authentication ensures the right level of access control based on risk, improving both cybersecurity and user experience.
Conduct Regular Authentication Audits and Reviews
- Continuous auditing of authentication systems helps identify vulnerabilities, outdated methods, and compliance gaps in cybersecurity frameworks.
- Regular reviews ensure authentication policies align with evolving regulatory standards, business growth, and threat landscapes.
Strengthen Cybersecurity Awareness Through User Training
- Employee awareness plays a critical role in preventing phishing attacks, credential theft, and social engineering threats.
- Ongoing cybersecurity training programs help users follow secure authentication practices and reduce insider risks.
Adopt Adaptive and Context-Aware Authentication
- Risk-based authentication evaluates user behavior, device, and location to enhance identity verification and prevent unauthorized access.
- Context-aware authentication improves security while maintaining a seamless and low-friction user experience.
Enable Mobile-First and Secure Authentication Access
- Mobile-friendly authentication methods, such as biometric authentication and push-based MF, support secure remote and hybrid work environments.
- Passwordless authentication improves usability and strengthens endpoint security across mobile devices.
Ensure Scalable and Future-Ready Authentication Solutions
- Scalable authentication systems support business growth through role-based access control, cloud integration, and automated user management.
- Flexible Identity and Access Management (IAM) solutions enable seamless integration with enterprise IT infrastructure and improve long-term cybersecurity resilience.
Conclusion
Choosing the right authentication method is a critical step in building a strong cybersecurity framework for modern businesses. As cyber threats such as phishing, credential theft, and ransomware continue to evolve, organizations must adopt advanced authentication solutions that ensure secure access, protect digital identities, and reduce cyber risk. Implementing best practices like Multi-Factor Authentication (MFA), Single Sign-On (SSO), passwordless authentication, and Identity and Access Management (IAM) strengthens access control while improving user experience and operational efficiency.
A well-defined authentication strategy not only enhances network security and data protection but also supports regulatory compliance, business continuity, and long-term scalability. Organizations that invest in modern authentication methods and proactive security measures are better equipped to prevent data breaches and maintain trust in an increasingly digital landscape.
CyberSec offers top IAM implementation services along with advanced cybersecurity solutions to help businesses secure their IT infrastructure, manage identities effectively, and stay ahead of evolving threats.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0