Cybersecurity Assessment Insights: Are You Really Protected from Modern Threats?
Explore how cybersecurity assessments help businesses across the GCC region identify vulnerabilities, manage cyber risks, and strengthen resilience against ransomware, data breaches, and evolving cyber threats with a proactive, risk-based security strategy.


Introduction
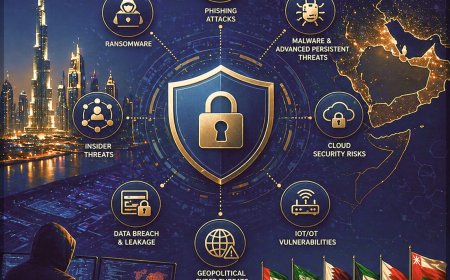
Cyber threats are accelerating at an unprecedented pace, and businesses across the GCC region (UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain) are increasingly becoming prime targets. Every minute, multiple organizations experience data breaches, ransomware attacks, phishing campaigns, and system compromises, making cyber incidents a persistent business risk rather than a rare event. Global cybercrime costs are projected to surpass $10.5 trillion annually, reinforcing the reality that no organization - regardless of size, sector, or geography - is immune to cyber threats. The critical question today is not if an attack will occur, but how prepared your organization is to detect, respond, and recover.
Recent threat intelligence highlights that a significant portion of cyber threat actor discussions and activities are focused on high-growth digital economies such as the UAE and Saudi Arabia. Rapid advancements in digital transformation, cloud adoption, artificial intelligence, and smart infrastructure initiatives have expanded the regional attack surface, making organizations more vulnerable to sophisticated cyberattacks.
Enterprises operating across the GCC must prioritize cybersecurity risk assessments, threat exposure management, vulnerability management, and proactive defense strategies to safeguard critical assets and maintain business continuity. Strengthening cyber resilience, compliance, and data protection frameworks is now essential to stay ahead of evolving adversaries in this high-risk environment.
Cybersecurity Assessment - A Business Imperative in the GCC Region

Organizations across the GCC region (UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain) must recognize that a cybersecurity assessment goes far beyond identifying weak passwords or outdated systems. A comprehensive assessment focuses on risk-based cybersecurity, helping businesses evaluate their attack surface, threat exposure, and overall security posture in an increasingly complex digital environment.
Effective cybersecurity begins by addressing critical questions:
- Where do your security vulnerabilities exist across cloud, network, and endpoints?
- What cyber threats are most relevant to your industry and region?
How resilient is your organization against ransomware attacks, data breaches, and advanced persistent threats (APTs)?
Many enterprises rely on existing security tools such as SIEM, EDR, and firewalls, assuming these controls provide complete protection. Reality proves otherwise. Cyber adversaries continuously evolve, leveraging zero-day vulnerabilities, misconfigurations, and identity-based attacks to bypass traditional defenses. Even minor security gaps can quickly become major exploitation points.
Identifying Vulnerabilities Before Attackers Do
Limited visibility into cyber risk and threat exposure often leaves organizations unaware of critical weaknesses until a breach occurs. A structured cybersecurity risk assessment enables proactive identification of hidden vulnerabilities across multi-cloud environments, SaaS applications, identity systems, and network infrastructure.
Security assessments uncover risks such as unpatched systems, cloud misconfigurations, weak access controls, shadow IT, and human errors, all of which contribute to increased attack surface risk. This proactive approach ensures that organizations strengthen their cyber resilience, compliance posture, and data protection frameworks before adversaries can exploit these gaps.
The True Cost of Cyber Risk in the GCC
Cyber incidents across the GCC extend far beyond technical disruption. Financial losses, regulatory penalties, legal liabilities, and reputational damage have become critical business concerns. Breaches involving personally identifiable information (PII), financial records, and sensitive enterprise data can significantly impact customer trust and long-term business growth.
Operational downtime, service outages, and business continuity failures further intensify the impact. A structured cybersecurity risk assessment and threat exposure analysis enables organizations to quantify risks using risk scoring models, threat intelligence, and business impact analysis, allowing leadership to make informed, strategic security investments.
Cybersecurity Gaps Increasing Business Risk Across the GCC Region
Unidentified and unaddressed security gaps expose organizations to financial loss, regulatory penalties, operational disruption, and reputational damage. A comprehensive cybersecurity assessment provides actionable insights, risk prioritization, and remediation strategies, enabling businesses across the GCC to build a secure, scalable, and future-ready cybersecurity posture.
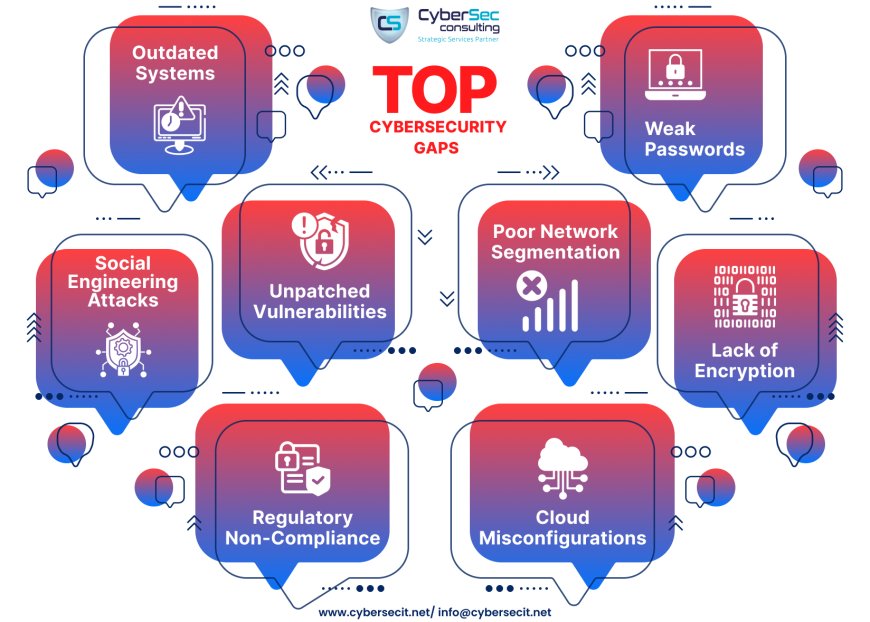
Enterprises across the GCC region (UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain) are experiencing rising exposure to cyber threats, data breaches, and ransomware attacks due to rapid digital transformation, cloud migration, and hybrid IT ecosystems. Expanding attack surface, multi-cloud environments, and SaaS adoption continue to introduce critical security gaps that weaken overall enterprise cybersecurity posture:
- Legacy systems and outdated infrastructure create high-risk entry points.
- Weak identity and authentication controls increase account compromise risks.
- Unpatched vulnerabilities expose systems to known exploits and malware.
- Poor network segmentation enables lateral movement across environments.
- Lack of encryption weakens data protection and privacy controls.
- Cloud misconfigurations expose sensitive data across SaaS and IaaS platforms.
- Social engineering and phishing attacks target human vulnerabilities.
- Regulatory non-compliance increases legal, financial, and operational risks.
Regulatory Compliance as a Strategic Priority
Organizations operating across the UAE and Saudi Arabia must comply with evolving data protection regulations, cybersecurity frameworks, and governance standards. Non-compliance can lead to fines, legal consequences, and loss of strategic partnerships.
A proactive cybersecurity compliance assessment helps identify gaps across data security, access management, governance, and risk frameworks, ensuring alignment with both regional regulations and global standards. Strong compliance posture enhances resilience and reduces audit risks.
Building Customer Trust in a Digital Economy
Digital-first economies across the GCC demand a stronger focus on data privacy, information security, and digital trust. A single data breach can significantly damage brand reputation and erode customer confidence. Protection of customer data, financial assets, and digital identities is now essential for sustainable growth.
Comprehensive cybersecurity assessments and data protection strategies ensure proper implementation of encryption, access controls, and security governance, reinforcing trust and safeguarding business relationships.
Aligning People, Process, and Technology
Human error remains a major contributor to cyber risk. A significant percentage of cyberattacks originate through phishing, social engineering, and credential theft. Advanced tools such as SIEM, EDR, and XDR cannot fully mitigate risks without strong security awareness, identity governance, and access control policies.
Cybersecurity assessments highlight gaps in employee training, identity and access management (IAM), privileged access management (PAM), and security awareness programs, ensuring a holistic approach to cybersecurity across people, processes, and technology.
Adapting to an Evolving Threat Landscape
Cyber adversaries continue to evolve, leveraging zero-day vulnerabilities, AI-powered attacks, advanced malware, and ransomware-as-a-service (RaaS) models. Static security frameworks quickly become ineffective in such a dynamic threat environment.
Continuous cybersecurity risk assessments, vulnerability management, and threat detection evaluations ensure that defense mechanisms remain effective. Organizations adopting proactive strategies achieve stronger cyber resilience, threat mitigation, and incident response readiness.
Identifying Hidden Vulnerabilities Before Exploitation
Perceived security maturity often masks critical hidden risks. Common exposures include unpatched systems, weak authentication, absence of multi-factor authentication (MFA), exposed cloud assets, and insufficient network segmentation.
A comprehensive cybersecurity vulnerability assessment and penetration testing (VAPT) approach uncovers these hidden weaknesses, enabling timely remediation. Proactive identification and mitigation of risks reduces breach likelihood and strengthens overall enterprise security posture across the GCC region.
Choosing the Right Cybersecurity Assessment Provider in the GCC Region

Organizations across the GCC region (UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain) must adopt a strategic approach when selecting a cybersecurity assessment provider. The effectiveness of any cybersecurity risk assessment, vulnerability assessment, or penetration testing (VAPT) depends heavily on the expertise, methodology, and capabilities of the provider. Asking the right questions ensures alignment with business objectives, regulatory compliance, and risk management goals.
Proven Industry Experience Matters
- Evaluate whether the provider understands industry-specific cyber risks, compliance requirements, and threat landscapes.
- Experience across similar sectors and business environments.
- Certified professionals holding CISSP, CEH, CISM, OSCP, or equivalent credentials.
- Demonstrated success in handling organizations of similar scale and complexity.
Adoption of Industry-Recognized Methodologies
- Reliable providers follow globally accepted frameworks such as NIST, ISO, and risk-based cybersecurity models.
- Comprehensive coverage of networks, applications, cloud, and data assets.
- Structured and holistic approach to attack surface management and threat exposure assessment.
Advanced Tools and Security Technologies
- Modern cyber threats require a combination of automated scanning and manual penetration testing.
- Real-world attack simulations, including red teaming and adversary emulation.
- Detailed and actionable reporting for risk remediation and mitigation strategies.
Client Reputation and Case Studies
- The credibility of a cybersecurity partner is reflected through client success stories and proven outcomes.
- Verified case studies across GCC markets.
- References demonstrating successful cybersecurity consulting and assessment services.
Independence and Unbiased Recommendations
- Objective assessments are critical for effective decision-making.
- Recommendations driven by risk exposure and business needs, not vendor affiliations.
- Transparent findings free from conflicts of interest.
Clear and Actionable Reporting
- Assessment outputs should support decision-making and execution.
- Structured reports including risk prioritization, threat intelligence insights, and remediation roadmaps.
- Post-assessment workshops or debrief sessions for implementation guidance.
Strong Compliance and Regulatory Alignment
- Organizations across the GCC must meet evolving data protection laws, cybersecurity frameworks, and regulatory standards.
- Coverage aligned to regional compliance mandates and global best practices.
- Support for audit readiness, compliance gap analysis, and governance frameworks.
Robust Threat Intelligence Capabilities
- Cyber threat landscape evolves rapidly across the Middle East.
- Continuous updates on emerging threats, zero-day vulnerabilities, and ransomware trends.
- Integration of threat intelligence platforms and real-time risk monitoring.
Incident Response and Cyber Resilience Support
- Preparation for cyber incidents is a critical component of any assessment.
- Availability of incident response services, SOC support, and threat containment strategies
- Defined response timelines and escalation mechanisms.
Transparent Pricing and Value Delivery
- Cybersecurity investments must deliver measurable outcomes.
- Clear pricing models aligned to scope, depth, and deliverables.
- No hidden costs, ensuring value-driven cybersecurity consulting and assessment services.
Selecting the right partner ensures that organizations across the GCC achieve proactive risk management, improved cyber resilience, and a stronger security posture, enabling them to stay ahead of evolving cyber threats while maintaining compliance and business continuity.
Why CyberSec Consulting Is the Right Cybersecurity Partner in the GCC Region?

CyberSec Consulting brings deep expertise across the GCC region (UAE, Saudi Arabia, Qatar, Oman, Kuwait, and Bahrain), delivering advanced cybersecurity consulting services, risk assessments, and threat exposure management tailored to regional business environments. Over the past three decades, more than 350+ organizations across government and private sectors have strengthened their cyber resilience, data protection, and regulatory compliance through our proven approach.
Extensive understanding of regional cyber threat landscapes, compliance frameworks, and industry-specific risks enables CyberSec Consulting to deliver solutions aligned to digital transformation, cloud security, and hybrid infrastructure challenges. Organizations benefit from a risk-based cybersecurity strategy that addresses evolving threats such as ransomware, zero-day vulnerabilities, identity-based attacks, and advanced persistent threats (APTs).
Standard security models often focus on reactive fixes, leaving critical gaps unaddressed. CyberSec Consulting adopts a proactive, intelligence-driven approach, combining cybersecurity assessments, vulnerability management, penetration testing (VAPT), and continuous threat monitoring to identify and remediate risks before they are exploited.
Customized security solutions, backed by real-time threat intelligence, attack surface management, and compliance alignment, ensure long-term protection and scalability. Focus remains on delivering actionable insights, measurable risk reduction, and enhanced security posture across complex IT environments.
Connect with a CyberSec Consulting security expert today to strengthen your cyber defense strategy, improve risk visibility, and stay ahead of evolving cyber threats in the GCC region.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0