AI-Driven Cyber Attacks in 2026: How LLMs Are Redefining Modern Cybersecurity Threats
Explore how AI-driven cyber attacks and LLMs are transforming the threat landscape, from phishing to polymorphic malware, and how AI-based cybersecurity solutions can defend modern enterprises.
Introduction

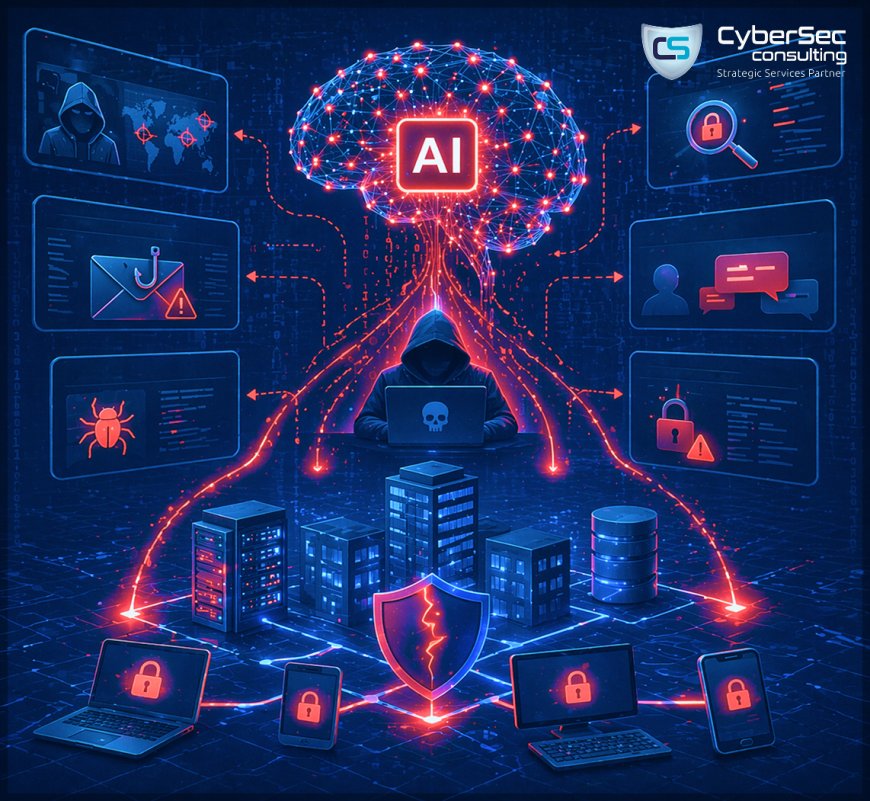
The modern cyberattack lifecycle has been significantly accelerated by artificial intelligence (AI) and generative AI technologies, making cyber threats faster, more sophisticated, and increasingly difficult to detect. Large Language Models (LLMs) are now being actively leveraged by threat actors to enhance cyberattack techniques, including automated reconnaissance, highly targeted AI-driven phishing attacks, rapid vulnerability discovery, proof-of-concept (PoC) exploit generation, and even AI-assisted malware development.
As these advanced capabilities continue to evolve, AI in cybersecurity is transforming the global threat landscape, creating complex challenges for security teams, SOC operations, and risk management strategies. Traditional defense mechanisms are no longer sufficient against these intelligent, adaptive threats.
This article explores how AI-powered cyberattacks are reshaping modern cybercrime, highlighting real-world use cases and attack methodologies enabled by LLMs. It also examines the growing impact of machine learning in cybersecurity, emphasizing why organizations must adopt proactive, intelligence-driven security frameworks.
The era of AI-driven cyber threats is no longer a future concern - it is already here, redefining how attackers operate and how enterprises must defend their digital environments.
AI-Powered Reconnaissance Techniques in Modern Cybersecurity Attacks

The reconnaissance phase of the cyberattack lifecycle has been significantly enhanced by artificial intelligence (AI) and machine learning in cybersecurity, enabling threat actors to gather intelligence faster and with greater precision. Advanced Persistent Threat (APT) groups are increasingly leveraging AI-driven reconnaissance techniques to automate the identification of high-value targets by analyzing organizational structures, business disclosures, and employee digital footprints across social platforms.
Using AI-powered threat intelligence, attackers can conduct large-scale network scanning, detect anomalies in traffic patterns, and identify potential vulnerabilities in IT infrastructure. These insights allow adversaries to refine their attack strategies, enabling highly targeted operations such as spear phishing, vishing, and social engineering campaigns based on behavioral patterns, such as executive travel schedules and communication habits.
Recent findings from leading cybersecurity research highlight how threat groups are utilizing Large Language Models (LLMs) and generative AI tools to enhance reconnaissance efforts and craft sophisticated attack campaigns. By combining AI capabilities with traditional open-source intelligence (OSINT) techniques, attackers are achieving deeper visibility into both public and private sector targets.
This evolution of AI in cyber threats demonstrates how reconnaissance is no longer manual but intelligent, automated, and highly effective - making early - stage attack detection more critical than ever for modern enterprises.
AI-Driven Phishing Attacks and Advanced Social Engineering Threats

The rise of AI-powered phishing attacks and advanced social engineering techniques is transforming the modern cyber threat landscape. By combining AI-driven reconnaissance with generative AI capabilities, threat actors are now able to launch highly targeted and scalable attacks with unprecedented precision. Advanced Persistent Threat (APT) groups are increasingly leveraging artificial intelligence in cybersecurity attacks to create convincing, context-aware phishing campaigns that significantly increase the success rate of breaches.
Through automated spear-phishing, attackers use insights gathered during reconnaissance to generate personalized, persuasive emails at scale. These AI-generated phishing campaigns mimic real communication patterns, making them difficult for traditional email security solutions to detect. In parallel, the use of deepfake technology in cybercrime has introduced a new level of risk, where AI-generated voice and video impersonations deceive individuals into sharing sensitive data or authorizing fraudulent transactions.
As machine learning and AI in cybersecurity threats continue to evolve, the realism and effectiveness of these attacks are outpacing legacy defense mechanisms. Even experienced professionals are finding it increasingly challenging to distinguish between legitimate interactions and AI-enabled cyber threats.
This shift highlights the urgent need for advanced threat detection, user awareness, and zero-trust security models to combat next-generation phishing and social engineering attacks.
AI-Based Vulnerability Discovery and Automated Exploitation Techniques

Artificial intelligence is rapidly transforming how cybercriminals identify and exploit security weaknesses, making AI-driven vulnerability discovery a critical concern in modern cybersecurity threat landscapes. Beyond reconnaissance and phishing, attackers are now leveraging machine learning in cybersecurity to automate the detection of software flaws, misconfigurations, and network vulnerabilities with unprecedented speed and accuracy.
Using advanced AI-powered exploit development, threat actors can analyze patches, perform reverse engineering, and uncover hidden security gaps that may lead to zero-day vulnerabilities. Emerging research and real-world demonstrations have shown that AI agents are capable of identifying potential zero-day exploits, highlighting a significant shift toward automated and intelligent attack methodologies.
In addition, generative AI tools enable attackers to create exploit code faster than traditional defense mechanisms can respond, increasing the risk of large-scale breaches. This acceleration in AI-enabled cyber attacks reduces the time between vulnerability discovery and exploitation, leaving organizations with limited response windows.
As AI in cyber threats continues to evolve, organizations must strengthen their vulnerability management, patch management, and threat detection strategies to defend against these next-generation risks. The growing use of AI in exploit development signals a future where cyber attacks become faster, smarter, and far more difficult to contain.
AI-Assisted Malware Development and Next-Generation Cyber Threats

The rapid advancement of artificial intelligence in cybersecurity threats has enabled attackers to accelerate malware development using AI-powered tools and Large Language Models (LLMs). While fully autonomous AI-generated malware is still evolving, threat actors are already exploiting generative AI platforms by bypassing built-in safeguards and leveraging specialized malicious AI models designed specifically for cybercrime.
These AI-driven cyber attack techniques allow attackers to generate, modify, and troubleshoot malicious code with greater speed and efficiency than ever before. Emerging underground tools and unrestricted AI chatbots are being used to automate vulnerability discovery, exploit development, and malware customization, significantly reducing the effort required to launch sophisticated attacks. In addition, attackers are leveraging AI to localize and adapt malware, enabling it to bypass regional cybersecurity defenses and detection systems.
The growing accessibility of advanced AI tools is accelerating the evolution of AI-powered malware, making it more adaptive, evasive, and difficult to detect using traditional security solutions. As machine learning in cyber attacks continues to mature, organizations face increasing risks from rapidly evolving threats that can outpace conventional defenses.
This shift highlights the urgent need for advanced endpoint security, threat intelligence, and proactive cybersecurity strategies to defend against next-generation AI-assisted malware attacks.
The Evolution of AI-Generated Polymorphic and Autonomous Malware

The next phase of AI-driven cyber threats is marked by the emergence of AI-generated polymorphic malware, a highly advanced form of malicious software that continuously changes its code to evade traditional signature-based detection systems. Powered by artificial intelligence and machine learning in cybersecurity, this evolving malware can dynamically modify its structure, making it significantly harder for legacy security tools to detect and contain. As a result, organizations must shift toward behavior-based threat detection, advanced endpoint security, and EDR solutions to effectively combat these threats.
Looking ahead, the rise of AI-powered autonomous malware represents an even more critical challenge for modern cyber defense strategies. Unlike conventional malware, these intelligent threats can operate independently, adapting in real time to bypass security controls, exploit system weaknesses, and optimize attack techniques. By leveraging reinforcement learning and AI-driven attack automation, such malware can continuously evolve, making incident response and threat mitigation increasingly complex.
This evolution signals a major shift in the cybersecurity threat landscape, where AI-enabled malware attacks become more sophisticated, persistent, and difficult to stop. Organizations must adopt proactive cybersecurity frameworks, zero-trust architecture, and continuous monitoring to defend against this next generation of intelligent and adaptive cyber threats.
Impact of AI on Threat Intelligence, Attribution, and Cyber Defense Strategy

The rise of AI-powered cyber attacks is creating significant challenges in threat attribution and cybersecurity intelligence. As artificial intelligence and machine learning in cyber threats continue to evolve, attackers can now mimic the tactics, techniques, and procedures (TTPs) of other threat actors, making it increasingly difficult to identify the true source of an attack. This advancement in AI-driven attack obfuscation is weakening traditional digital forensics and threat intelligence frameworks.
By leveraging AI-enabled deception techniques, adversaries can confuse forensic investigations, disrupt coordinated cyber defense strategies, and reduce the effectiveness of global intelligence-sharing efforts. This is particularly critical for collaborative security alliances that rely on accurate attribution to respond effectively to emerging threats. As a result, incident response, cyber threat analysis, and national cybersecurity planning become more complex and resource-intensive.
Accurate attribution plays a vital role in understanding attacker intent, identifying targeted industries, and predicting future attack patterns. However, with the increasing use of AI in cybercrime, defenders are often forced to prepare for multiple threat scenarios, complicating risk management and security operations.
This growing challenge highlights the need for advanced threat intelligence platforms, behavioral analytics, and AI-driven cybersecurity solutions to enhance visibility and improve attribution accuracy in an increasingly complex threat landscape.
Conclusion
Artificial intelligence is fundamentally reshaping the cybersecurity landscape, transforming how cyber attacks are executed across every stage of the attack lifecycle. From AI-driven reconnaissance and phishing to automated vulnerability exploitation and adaptive malware, threat actors are leveraging LLMs and generative AI to operate with unprecedented speed, scale, and precision.
Standard security models are no longer sufficient to defend against these AI-powered cyber threats. Organizations must adopt proactive, intelligence-driven cybersecurity strategies, including advanced threat detection, behavioral analytics, zero trust architecture, and continuous monitoring to stay resilient against evolving risks.
As cyber threats become more intelligent and autonomous, the need for AI-enabled cybersecurity solutions becomes critical for modern enterprises.
CyberSec Consulting offers AI-based cybersecurity services and service-based solutions designed to help organizations detect, prevent, and respond to next-generation cyber threats while strengthening their overall security posture.
What's Your Reaction?
 Like
0
Like
0
 Dislike
0
Dislike
0
 Love
0
Love
0
 Funny
0
Funny
0
 Angry
0
Angry
0
 Sad
0
Sad
0
 Wow
0
Wow
0