

Modern digital systems generate massive volumes of operational and security data every second. However, many incident response workflows still operate reactively, treating each outage or security incident as an isolated emergency. An alert is triggered, teams rush to contain the issue, services are restored, dashboards turn green—and valuable lessons are often lost. Meanwhile, the same failure patterns quietly resurface across application logs, system metrics, cloud environments, CI/CD pipelines, and support tickets, eventually leading to the next “unexpected” incident or security breach.
An AI-powered continuous operations loop breaks this repetitive cycle by transforming incident response into an intelligent, learning-driven process. Instead of closing incidents and moving on, this approach continuously captures incident data, root causes, response actions, and outcomes. That intelligence is then fed back into AI models, security analytics, automation workflows, and incident response playbooks, enabling systems to improve with every event.
For AI-driven cybersecurity operations, SOC teams, and cloud security environments, this model delivers a shift from reactive firefighting to proactive risk reduction. It enhances threat detection and response (TDR), reduces manual intervention, improves mean time to detect (MTTD) and mean time to respond (MTTR), and strengthens overall cyber resilience.
For organizations adopting AI-first security operations, SOAR, SIEM, and automated incident management, a continuous AI operations loop ensures that every incident—whether operational or security-related—becomes a source of actionable intelligence. The result is smarter systems, more effective automation, and a continuously improving security posture that stays ahead of evolving cyber threats.

Incident Management is the structured, end-to-end discipline that governs how organizations identify, assess, prioritize, respond to, and learn from operational and security incidents. It ensures service continuity, minimizes business impact, and strengthens long-term resilience across IT, cloud, and cybersecurity environments.
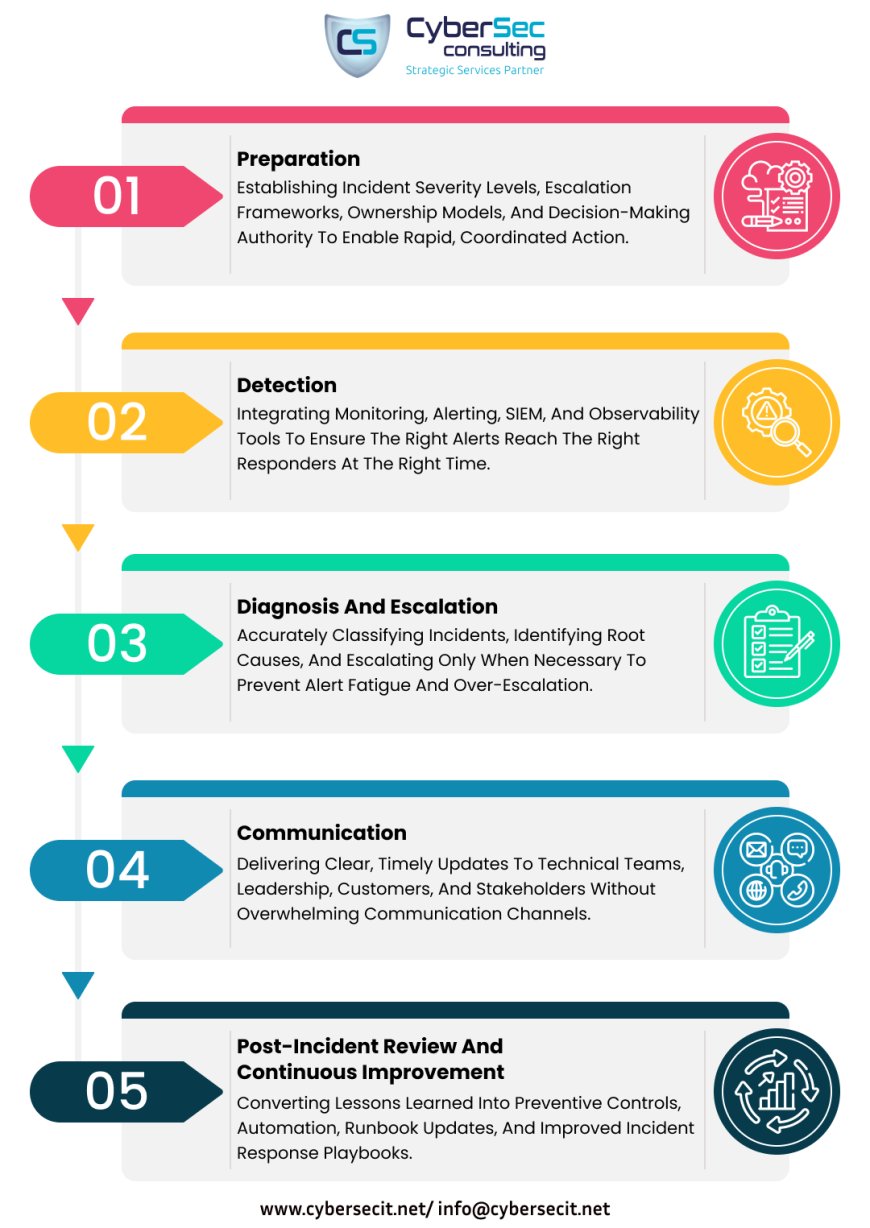
Unlike incident response, which focuses on immediate containment and remediation, Incident Management spans the entire incident lifecycle, including:

Many traditional incident management processes fail to retain knowledge once an incident is resolved. Crucial details are scattered across system logs, chat threads, ticketing tools, and incomplete post-incident reports. When similar incidents occur weeks or months later, response teams are forced to start from zero, reconstructing timelines, reanalyzing root causes, and relying on informal tribal knowledge rather than actionable insights.
This creates a recurring operational bottleneck. As IT and cloud environments scale, incident frequency rises. Increased alert volume leaves teams with little time for proactive improvements, which in turn leads to more outages, security incidents, and service disruptions. Over time, this cycle results in mounting operational debt, increased on-call fatigue, longer mean time to resolution (MTTR), and higher risk exposure for the business.
A learning-driven incident management approach breaks this pattern. Instead of treating incidents as isolated events, it continuously captures and preserves intelligence across the entire incident lifecycle - detection, triage, root cause analysis, escalation, communication, remediation, and post-incident review. This structured knowledge is then fed back into automation, runbooks, AI models, and response workflows, enabling faster, smarter, and more consistent incident handling.
By transforming incidents into reusable insights, organizations can reduce repeat failures, improve SOC efficiency, strengthen cyber resilience, and shift from reactive firefighting to proactive incident prevention.
A constant operations loop transforms every incident into actionable intelligence, enabling systems to learn, adapt, and improve with each operational event. Rather than treating incidents as isolated disruptions, this model creates a feedback-driven process that strengthens reliability and resilience over time.
As this feedback loop matures, routine incidents are automatically detected and resolved, significantly reducing mean time to resolution (MTTR) and alert fatigue. Security and operations teams can shift their focus toward higher-value initiatives, such as threat prevention, reliability engineering, and process optimization.
Post-incident reviews become data-driven and efficient, starting with pre-built summaries and AI-enriched insights rather than fragmented notes. Over time, organizations achieve greater operational resilience, SOC efficiency, and service reliability through continuous, incremental learning instead of reactive, one-off retrospectives.
Modern incident response teams rely on systems that deliver accurate, complete, and continuously updated operational context. When incident data is scattered across tools, chats, and logs, even advanced AI-powered incident management platforms struggle-often amplifying alert noise instead of reducing it.
A learning-driven incident management model addresses this challenge by ensuring that every incident, whether minor or critical, feeds structured intelligence back into the system. Over time, this creates a reliable operational knowledge base that strengthens IT operations, SRE practices, and AIOps workflows.
This approach creates a persistent operational memory - the foundation AI systems need to guide, predict, and automate incident response effectively. Without consistent, structured data, AI tools operate on incomplete signals, limiting their ability to reduce mean time to detect (MTTD) and mean time to resolve (MTTR).
Organizations that adopt this model see measurable impact. For example, TUI reduced incident recovery times by up to 90% by capturing, standardizing, and reusing response playbooks across its global travel infrastructure - demonstrating the real business value of learning-based incident management and automation.
Cloud-native architectures and evolving cyber threats, incident management can no longer remain reactive or siloed. Organizations that treat incidents as one-time disruptions miss a critical opportunity to learn, adapt, and strengthen their security and operational posture. A learning-driven, AI-powered incident management model changes this narrative by converting every operational and cybersecurity incident into actionable intelligence.
By embedding a continuous AI operations loop, enterprises gain persistent operational memory, faster detection and response, reduced alert fatigue, and measurable improvements in MTTD and MTTR. More importantly, teams move away from firefighting toward proactive risk mitigation, resilience engineering, and compliance-driven governance. Incidents stop being liabilities and instead become inputs that continuously enhance automation, response playbooks, and decision-making across SOC, IT operations, cloud security, and AIOps environments.
CyberSec helps organizations operationalize this modern incident management approach through Incident Management and Incident Response services delivered under its Compliance and Risk Management framework. Our services enable enterprises to:
Whether you are enhancing SOC maturity, aligning with regulatory requirements, or strengthening enterprise resilience, CyberSec empowers your teams to transform incidents into insights and risks into resilience.
Connect with CyberSec today to implement a learning-driven incident management and response strategy that protects your business, ensures compliance, and prepares you for the threats of tomorrow.
For More Updates on CyberSecurity Insights & Trends: Visit CyberSec Consulting
Copyright © 2026 CyberSec Consulting - All Rights Reserved