Introduction
Data privacy is a common practice for how data is collected and handled. Data is usually stored with permissions based on their sensitivity and importance. Data privacy primarily lies in the permissions. It's typically applied to the organization's health, identity, and finance. It ensures that only approved individuals are allowed to access data.
Seeing so many data breaches, data privacy has become a serious concern for many organizations. Not only the big players but also mid-size organizations hold a tremendous amount of sensitive data. Since it safeguards personal integrity, build trust in the virtual world. Industries often face difficulties in complying with data privacy regulations. As they hold strict policies that need to be adhered to protect data. Industries need to demonstrate their data privacy practices to build a solid reputation.
When organizations create a strong trust, users are more likely to willingly to share their personal information. Numerous data protection laws, such as GDPR (General Data Protection Regulation) and Federal Decree-Law. It requires industries to carry out measures to protect their users' data privacy rights.
Importance of Data Privacy

- Safeguarding Personal and Sensitive Data - Data privacy plays a critical role in protecting personal and sensitive information from unauthorized access, data breaches, and cyber threats. This includes safeguarding financial records, health data, identity details, and confidential business information. Strong data privacy controls help reduce risks such as identity theft, fraud, and data misuse—key concerns in today’s digital economy.
- Building Trust and Digital Confidence - Data privacy is foundational to trust between organizations and their customers. When businesses demonstrate a strong commitment to data protection, they enhance credibility and foster long-term customer confidence. Trusted organizations are better positioned to strengthen customer relationships, protect brand reputation, and sustain business growth.
- Ensuring Regulatory and Compliance Readiness - Global data protection regulations such as GDPR, CCPA, ISO 27001, and regional privacy laws mandate strict controls over personal data handling. Implementing compliant data privacy frameworks helps organizations avoid legal penalties, regulatory scrutiny, and reputational damage while maintaining operational continuity.
- Promoting Ethical and Transparent Data Practices - Responsible data handling is both a legal and ethical obligation. Organizations must ensure informed consent, data minimization, and transparent usage policies. Ethical data privacy practices demonstrate accountability and respect for individual rights, reinforcing organizational integrity.
- Enabling Secure Data-Driven Innovation - Effective data privacy strategies encourage innovation by creating a secure environment where individuals feel confident sharing information. This trusted data ecosystem supports advanced analytics, personalization, and digital transformation initiatives without compromising security.
- Empowering Individuals Through Data Control - Data privacy gives individuals control over how their personal information is collected, processed, and shared. Respecting user autonomy prevents exploitation and ensures fair, responsible use of data across digital platforms.
CyberSec Consulting delivers comprehensive data privacy and cybersecurity solutions to help organizations protect sensitive data, achieve regulatory compliance, and mitigate cyber risks. Through privacy assessments, data protection frameworks, encryption solutions, risk management, and managed security services, CyberSec Consulting enables businesses to build secure, compliant, and future-ready data protection strategies.
Data Privacy Matters: Building Trust, Security, and Digital Resilience
- Data privacy has become a critical business and societal priority. Organizations collect, process, and store vast volumes of personal and sensitive information—ranging from customer identities and financial records to health data and intellectual property. Protecting this information is no longer optional; it is essential for trust, compliance, and long-term business success.
- Data privacy ensures that individuals maintain control over how their personal information is collected, used, and shared. When privacy is respected, the risks of identity theft, fraud, and data misuse are significantly reduced. At the same time, organizations benefit from stronger customer confidence and improved brand reputation. In fact, businesses that prioritize data protection and privacy are far more likely to retain customers and build long-term loyalty in a competitive digital marketplace.
- From a regulatory perspective, global laws such as GDPR, CCPA, and regional data protection regulations require organizations to implement strong privacy controls and security mechanisms. Non-compliance can lead to severe financial penalties, legal action, and reputational damage. This makes privacy-driven security strategies a foundational element of modern cybersecurity services.
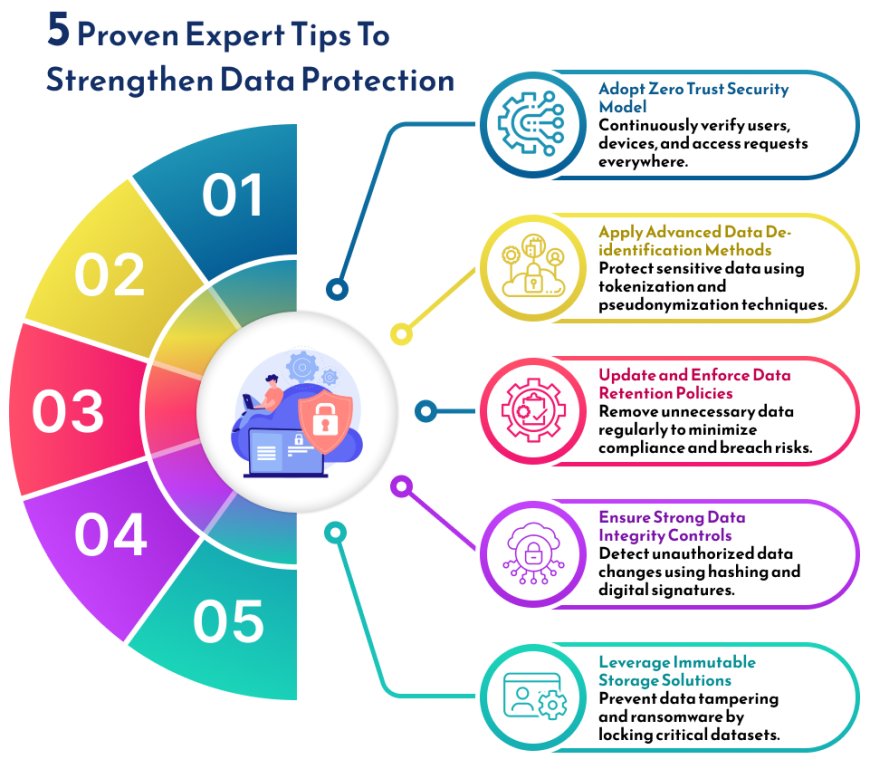
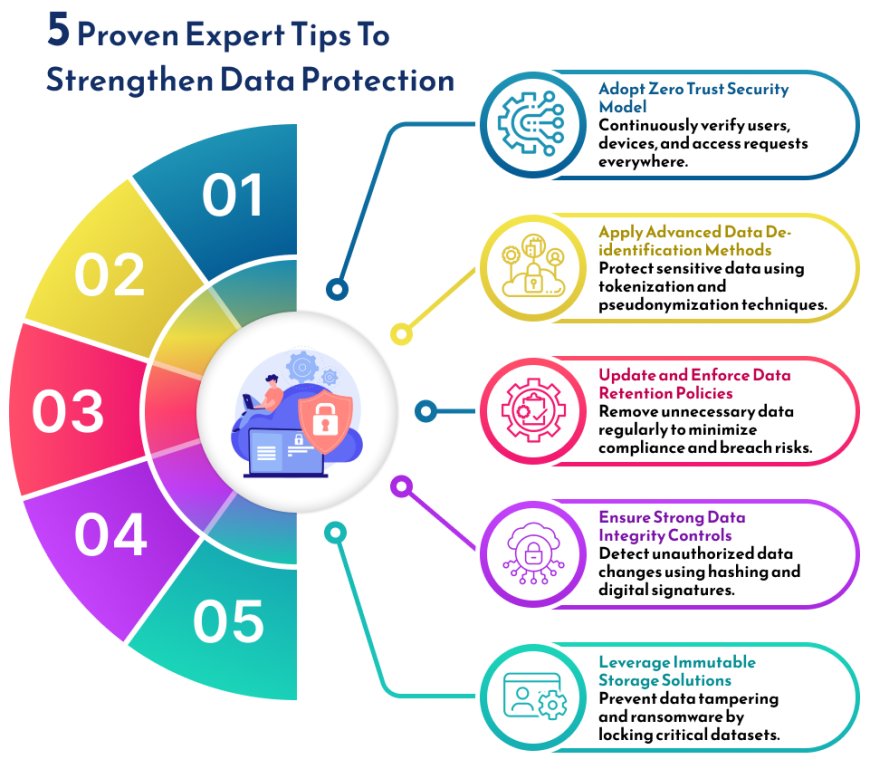
Tips to Strengthen Your Data Protection
Data Protection vs. Data Privacy: Understanding the Difference
While data privacy and data protection are closely related and often used interchangeably, they serve distinct but complementary purposes in a modern cybersecurity strategy. Both are essential for safeguarding sensitive information and maintaining digital trust.
- Policies vs. Security Mechanisms -
- Data privacy focuses on defining who is authorized to access data and how that data can be used. It establishes the policies, rules, and consent frameworks that govern data usage. In contrast, data protection refers to the technical and operational controls, such as encryption, access controls, monitoring, and incident response, that enforce those privacy policies.
- Simply creating data privacy policies does not automatically prevent unauthorized access. Likewise, deploying security tools without clear privacy guidelines may restrict access but still expose sensitive data to misuse. A strong cybersecurity posture requires both privacy policies and protection mechanisms working together.
- User Control vs. Organizational Responsibility -
-
- Data privacy is largely driven by individuals, who decide how their personal information is collected, shared, and processed. Data protection, however, is the responsibility of organizations that store and manage this information. Companies must implement robust information security and data protection controls to ensure privacy preferences are respected.
- Global regulations such as GDPR, CCPA, and other data protection laws reflect this distinction, placing accountability on organizations to honor user privacy rights through effective protection measures.
Conclusion
- Data privacy regulations continue to evolve, and the exchange of sensitive information accelerates; organizations must act proactively to protect personal data and remain compliant. CyberSec Consulting empowers businesses to meet global privacy requirements with confidence through comprehensive data privacy and data protection services.
- Don’t wait for a compliance challenge or data breach to take action. Partner with CyberSec Consulting to build a secure, compliant, and future-ready data privacy strategy that protects your organization and earns customer trust.
Connect with CyberSec Consulting to explore our data privacy services and solutions, and learn more about data protection and privacy.
For More Information, Click on - Data Privacy
Case Study - Tackling Data Transfer Challenges to Secure Organization-Sensitive Information
For More Updates on CyberSecurity Insights & Trends: Visit CyberSec Consulting