
With extensive experience and unmatched expertise in identifying vulnerabilities across the entire spectrum, CyberSec Consulting excels in network security penetration testing. Our capabilities range from uncovering critical vulnerabilities to addressing even the most minor security gaps within your network.
At the core of our penetration testing process is a robust methodology aligned with globally recognized industry standards, including NIST, OWASP, SANS, and OSSTMM. This ensures that our testing procedures adhere to best practices, delivering a thorough and systematic evaluation of your network's security posture.

Our security consultants replicate various real-world attack vectors to identify potential vulnerabilities. This includes testing for issues such as SQL injection, cross-site scripting, and other threats.
We prioritize identified vulnerabilities based on their severity and potential impact, enabling your organization to focus on resolving the most critical issues first. This ensures optimal resource allocation for addressing risks effectively.
We go beyond quantifying risks by providing actionable insights into how vulnerabilities could impact your operations, data integrity, and reputation.
Our process doesn’t stop at identifying flaws. We provide tailored remediation strategies, actionable recommendations, and guidance to implement robust security measures that strengthen your network against future threats.
CyberSec Consulting employs globally accepted methodologies like the Penetration Testing Execution Standard (PTES) to ensure a thorough and effective assessment. Our network security testing process includes the following steps:

Comprehensive discovery of all accessible systems and their associated services to gather maximum information.

Identification of vulnerabilities using a combination of automated scans and deep-dive manual testing techniques.

Detailed documentation and analysis of identified vulnerabilities to formulate an effective attack plan.

Execution of the plan to exploit vulnerabilities and assess the real-world impact on your systems.

Detailed reporting of overall risks, including strengths and weaknesses of your security posture, for all stakeholders.
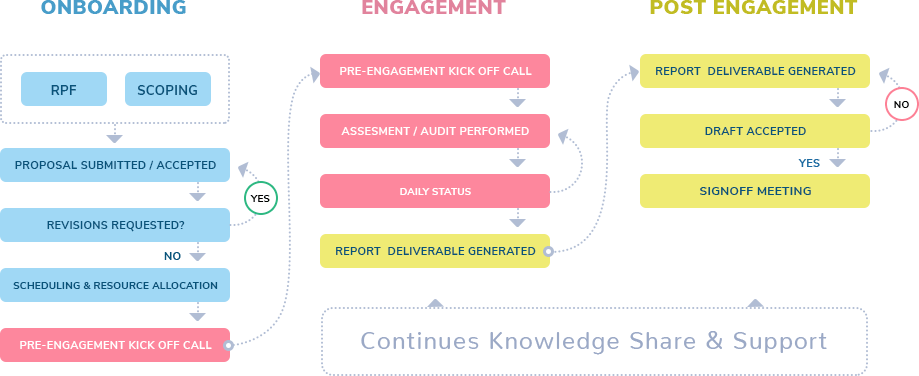
At CyberSec Consulting, we follow the following engagement workflow for working with the clients.

Wireless networks, including those using WPA2, WEP, and EAP protocols, are vulnerable to attacks that can expose an organization’s network. CyberSec Consulting identifies potential vulnerabilities starting from wireless LAN controllers to individual wireless devices.

We ensure host operating systems are secure by reviewing configurations, applying the latest security patches, and implementing best practices to fortify system defenses.
CyberSec Consulting performs a comprehensive review of your network architecture to identify gaps in existing security controls. We provide recommendations to strengthen your architecture and align it with your organization’s security objectives.